RESEARCH OUTLINE
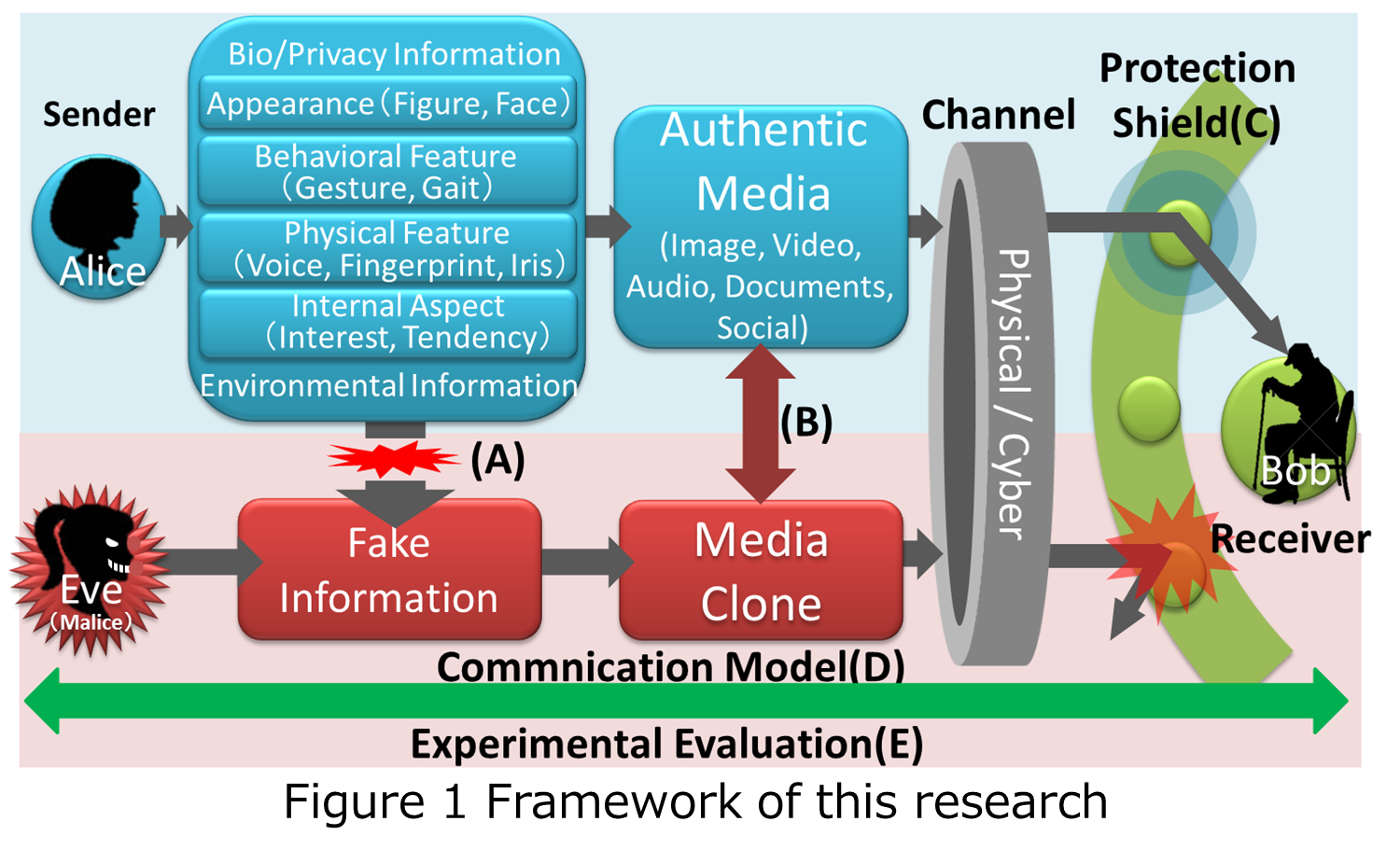 Figure 1 shows a
framework of this research. A sender Alice sends her authentic media such as
video or audio to a receiver Bob through physical and cyber channels. At this
time, a malicious sender Eve stealthily acquires privacy, biological, and
environmental information of Alice, to make fake information. Based on the fake
information, she generates Alice's media clones and sends them to Bob to
deceive him.
Figure 1 shows a
framework of this research. A sender Alice sends her authentic media such as
video or audio to a receiver Bob through physical and cyber channels. At this
time, a malicious sender Eve stealthily acquires privacy, biological, and
environmental information of Alice, to make fake information. Based on the fake
information, she generates Alice's media clones and sends them to Bob to
deceive him.
To realize a communication system for defending the receivers attacked
by the media clones, we pursue the following five topics.
[PDF]
(A) Development of methods for protecting the privacy,
biological, and environmental information to prevent fake information generation.
(B) Verification of the capability of generating various types of media clones such as
audio, visual, text,
and social media
derived from the fake information.
(C) Realization of
a protection shield for media clones’ attacks by recognizing them. We focus
on analysis of liveness
resulting from biological living features.
(D) Modeling of the proposed communication system.
(E) Experimental evaluation
for a total system and its components. We build and open to the public
a benchmark
database of both authentic media and media clones.